How To Lock And Protect Away Secret Files With GNU Privacy Guard
This can be a simple text file, or a zip file containing many files, or an archive file (tar). If that makes no sense, browse the web and in five minutes you can find out how to navigate the file system specific to your operating system (search: “YouTube browsing file system command prompt” and include your operating systems name). You can clear it like this: gpg-connect-agent reloadagent/ byeOnce your file is encrypted, the original file will remain (unencrypted), and a new file will be developed. You can then rename the file if you want, or you could have called the file by including additional options in the command above, like this: gpg -c– output MySecretFile.txt file.txtHere, we have “gpg”, a space, “-c”, a space, “– output”, a space, the filename you want, an area, the name of the file you are encrypting.Its a great idea to practice decrypting the file. In this case, a brand-new file is not developed, but the contents of the file are printed to the screen.You can likewise decrypt the file and specify the output files name like this: gpg -d– output file.txt file.txt.gpgHere we have “gpg”, an area, “-d” which is not strictly required, an area, “– output”, an area, the name of the new file we desire, an area, and lastly the name of the file we are decrypting.Sending The Encrypted FileYou can now copy this file to a USB drive, or email it.
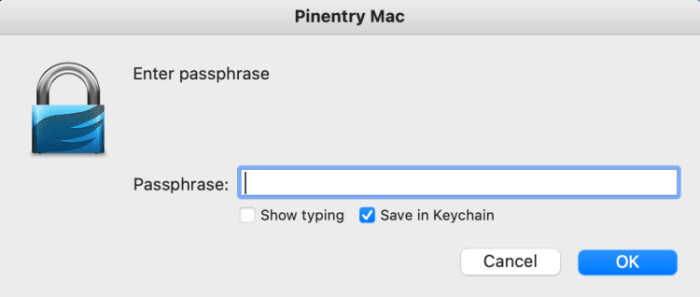
In this guide, I will discuss the options at hand for encrypting files using open-source software on a Linux, Mac, or Windows computer. You can then carry this digital details across distance and time, to yourself or others.The program “GNU Privacy Guard” (GPG) an open-source variation of PGP (Pretty Good Privacy), permits: Encryption utilizing a password.Secret messaging utilizing public/private crucial cryptographyMessage/Data authentication (utilizing digital signatures and confirmation)Private essential authentication (used in Bitcoin)Option OneOption one is what Ill be showing listed below. You can encrypt a file utilizing any password you like. Any individual with the password can then open (decrypt) the file to view it. The issue is, how do you send out the password to somebody in a secure way? Were back to the initial problem.Option TwoOption two resolves this predicament (how-to here). Rather of locking the file with a password, we can lock it with someones public secret– that “somebody” is the intended recipient of the message. The general public key originates from a matching personal secret, and the personal key (which just the “someone” has actually) is utilized to unlock (decrypt) the message. With this approach, no delicate (unencrypted) information is ever sent. Extremely nice!The public key is something that can be distributed over the internet safely. Mine is here. They are usually sent to keyservers. Keyservers resemble nodes that save public secrets. They keep and integrate copies of individuals public secrets. Heres one: Ubuntu KeyserverYou can enter my email and discover my public type in the result. Ive likewise stored it here and you can compare what you discovered on the server.Option ThreeOption 3 is not about secret messages. It is about inspecting that a message has actually not been modified throughout its delivery. It works by having somebody with a private key indication some digital information. The data can be a letter or even software. The process of signing creates a digital signature (a large number originated from the personal key and the data thats getting signed). Heres what a digital signature looks like: Its a text file that starts with a “begin” signal, and ends with an “end” signal. In in between is a bunch of text that actually encodes a huge number. This number is stemmed from the personal key (a huge number) and the data (which is actually constantly a number also; all data is ones and nos to a computer system). Anyone can validate that the information has not been changed since the original author signed it by taking the: Public keyDataSignatureThe output to the question will be FALSE or real. TRUE methods that the file you downloaded (or message) has actually not been modified given that the developer signed it. Extremely cool! Incorrect methods that the information has actually changed or the incorrect signature is being applied.Option FourOption four is like alternative three, other than that instead of checking if the data has not been customized, then TRUE will imply that the signature was produced by the private secret associated with the general public essential used. Simply put, the person who signed has the personal secret to the general public secret that we have.Interestingly, this is all that Craig Wright would have to do to show he is Satoshi Nakamoto. He doesnt have to in fact spend any coins.We already have the addresses (similar to public keys) that are owned by Satoshi. Craig can then produce a signature with his private secret to those addresses, integrated with any message such as “I truly am Satoshi, haha!” and we can then integrate the message, the signature, and the address, and get a TRUE outcome if he is Satoshi, and a CRAIG_WRIGHT_IS_A_LIAR_AND_A_FRAUD result if he isnt. Alternative Three And Four– The Difference.Its actually a matter of what you trust. If you trust that the sender owns the private key to the public key you have, then verification checks that the message has not changed.If you dont trust the private crucial/ public key relationship, then verification is not about the message altering, but the essential relationship.Its one or the other for a FALSE result.If you get a TRUE result, then you know that BOTH the essential relationship stands, AND the message is unaltered because the signature was produced.Get GPG For Your ComputerGPG already features Linux os. If you are unfortunate adequate to be utilizing a Mac, or God forbid a Windows computer, then youll require to download software application with GPG. Guidelines to download and how to utilize it on those operating systems can be discovered here.You do not need to utilize any of the graphical elements of the software, everything can be done from the command line.Encrypting Files With A PasswordCreate the secret file. This can be a basic text file, or a zip file containing many files, or an archive file (tar). Depending upon how delicate the data is, you may think about developing the file on an air-gapped computer system. Either a desktop computer constructed without any WiFi parts, and never ever to be linked to the internet by cable, or you can develop a Raspberry Pi Zero v1.3 really cheaply, with instructions here.Using a terminal (Linux/Mac) or CMD.exe (Windows), alter your working directory to any place you put the file. If that makes no sense, browse the internet and in 5 minutes you can find out how to navigate the file system specific to your operating system (search: “YouTube browsing file system command trigger” and include your operating systems name). From the proper directory, you can encrypt the file (“file.txt” for instance) like this: gpg -c file.txtThats “gpg”, a space, “-c”, a space, and then the name of the file.Youll then be prompted for a password. This will secure the brand-new file. If youre using GPG Suite on the Mac, see the “Save in Keychain” is inspected by default (see listed below). You may want to not save this password if its particularly sensitive.Whichever OS you utilize, the password will be saved for 10 minutes to the memory. You can clear it like this: gpg-connect-agent reloadagent/ byeOnce your file is encrypted, the original file will stay (unencrypted), and a new file will be developed. You need to decide if you will delete the initial or not. The brand-new files name will be the exact same as the initial however therell be a “. gpg” at the end. For instance, “file.txt” will produce a new file called “file.txt.gpg”. You can then rename the file if you want, or you could have named the file by adding extra choices in the command above, like this: gpg -c– output MySecretFile.txt file.txtHere, we have “gpg”, a space, “-c”, an area, “– output”, an area, the filename you want, a space, the name of the file you are encrypting.Its an excellent idea to practice decrypting the file. This is one method: gpg file.txt.gpgThis is just “gpg”, an area, and the name of the encrypted file. You do not require to put any options.The GPG program will guess what you mean and will attempt to decrypt the file. If you do this instantly after securing the file, you may not be prompted for a password since the password is still in the computer systems memory (for 10 minutes). Otherwise, youll need to enter the password (GPG calls it a passphrase). You will notice with the “ls” command (Mac/Linux) or “dir” command (Windows), that a new file has been developed in your working directory site, without the “. gpg” extension. You can read it from the command trigger with (Mac/Linux): feline file.txtAnother way to decrypt the file is with this command: gpg -d file.txt.gpgThis is the same as before however with a “-d” choice. In this case, a new file is not developed, but the contents of the file are printed to the screen.You can also decrypt the file and define the output files name like this: gpg -d– output file.txt file.txt.gpgHere we have “gpg”, a space, “-d” which is not strictly required, a space, “– output”, an area, the name of the new file we desire, a space, and lastly the name of the file we are decrypting.Sending The Encrypted FileYou can now copy this file to a USB drive, or email it. It is secured. Nobody can read it as long as the password is good (long and complex enough) and cant be cracked.You might send this message to yourself in another country by storing it in e-mail or the cloud.Some silly individuals have stored their Bitcoin private secrets to the cloud in an unencrypted state, which is extremely dangerous. If the file including Bitcoin personal secrets is encrypted with a strong password, its safer. This is specifically true if its not called “Bitcoin_Private_Keys. txt.gpg”– Dont do that!WARNING: Its essential to understand that in no method am I motivating you to put your Bitcoin private key info on a computer (hardware wallets were developed to permit you to never ever need to do this). What I am explaining here is for special cases, under my guidance. My students in the mentorship program will understand what they are doing and will just use an air-gapped computer, and understand all the prospective risks and issues, and methods to avoid them. Please do not type seed phrases into a computer system unless you are a security expert and know exactly what you are doing, and do not blame me if your bitcoin is stolen!The encrypted file can also be sent to another person, and the password can be sent out individually, perhaps with a different communication device. This is the easier, and less safe method, compared to choice two explained at the beginning of this guide.There are in fact all sorts of methods you can construct the delivery of a secret message across distance and time. If you know these tools, believe tough and thoroughly about all the risks and circumstances, a good plan can be made. Or, I am readily available to assist.Good luck, and pleased Bitcoining!This is a visitor post by Arman The Parman. Opinions expressed are completely their own and do not necessarily show those of BTC Inc or Bitcoin Magazine.