Adversarial Thinking And Ways To Attack Bitcoin
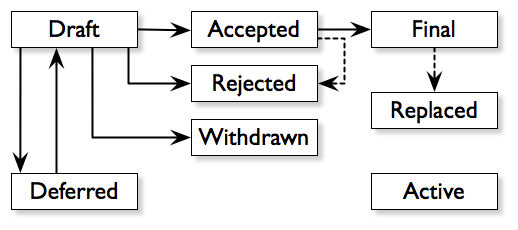
Bitcoin 2022, hosted in Miami, Florida, on April 6-9, featured a panel entitled “Preventing Attacks on Bitcoin” with three Bitcoin Core designers: Luke Dashjr, Bryan Bishop and Jameson Lopp (replacementing for Peter Todd). The panel was moderated by Shinobi.The panelists go over technical and social attack vectors, mostly in the development process of Bitcoin Core, that might impede or entirely derail Bitcoins sole objective as immutable money. The purpose for freely conceptualizing attack vectors is to create suitable defense procedures and, as Sun Tzus “The Art of War” strategizes:”Do not trust that the enemy isnt coming. Trust your preparedness to satisfy him. Do not trust that the opponent wont attack. Rely just on your ability to select a location that the enemy cant attack.”The following is a summary of said panel with a quick overview of the Bitcoin Core advancement process.Brief Bitcoin Core OverviewThe Bitcoin Core developers resolve an advancement process to provide the Bitcoin protocol bug spots, software application optimizations and improved functions; they then release these updates following community consensus through Bitcoin Improvement Proposals (BIPs). To successfully craft an attack against the advancement process, on either a technical or social level, would possibly hamper (in some cases vital) procedure updates and instill suspect between developers. To clarify, Bitcoin Core is a totally free and open-source software application of a Bitcoin full node, described as a client. Although deceiving in name, Bitcoin Core does not have centralized or “core” control over the Bitcoin network, but rather functions as simply one possible client that people are complimentary to utilize at their discretion. Too, the Bitcoin protocol consensus rules need that all Bitcoin full nodes and financial participants invariably enforce those guidelines when thinking about the credibility of a block.Additionally, Bitcoin Core updates are not downloaded instantly but rather by hand, as automated software application updates offer an attack vector for a naughty star to jeopardize all the nodes and miners in a single stroke.The Bitcoin Core group of designers do not pedestal a single leader or representative– hence distancing the client and development procedure from individual character exploitation due to faults all earthly leaders naturally have. Narcissistic leaders can be damaged by developing discontent within their fan base, or short-tempered leaders can act crazily when provoked with insults. To overturn an upstart movement, one must cleverly deal with its leader or fracture their following.Yet without a single leader, how do independent Bitcoin Core developers come to contract on complex design choices or emergency bug fixes? The abovementioned BIPs are utilized in the Bitcoin Core advancement procedure to implement features or info to the Bitcoin procedure, but BIPs also work to standardize the communication of originalities, as diagrammatically depicted listed below and as explained in BIP 1: BIP workflowHow can we throw a wrench into this process? In spite of presenting some procedure through BIP 1 into an otherwise unstructured network, there presents a chance for just misguided or malicious stars to overturn the development procedure through both social and technical ways. Recognizing this “wrench” nevertheless is typically only possible in hindsight– making specific attack vectors specifically hard to find and avoid. If you can evade a wrench, you can dodge a deviant developer determined on pushing their self-serving program at Bitcoins expense.In practice, actual BIP executions are not as neat as a workflow diagram and the above explanation has been abridged. We can start to theorize wicked methods to subvert the decentralized development process.Note: The term “consensus” is an ambiguous word used to imply a number of various things beyond the guidelines of Bitcoin. Normally used to suggest “everybody basically agrees” on a choice while, in truth, there are more accurate, unique words that work to much better define the differing levels of agreement on a choice than the catch-all term “agreement.” For simplenesss sake, this article refers to near-unanimous and basic arrangement as attaining “agreement.”Former Attacks On BitcoinThe Bitcoin network released in 2009 with several crucial bugs and oversights that could have resulted in severe technical attack vectors, however those publicly-known vulnerabilities were remedied long back. Normally speaking, these oversights and bugs are difficult to find as there is absolutely nothing in the code that is obtrusively or painfully obvious. A dedicated open-source development neighborhood willingly contributing to the codebase has actually worked persistently to improve the protocols integrity over the previous years and then some. By understanding previous vulnerabilities and their services, we can stay watchful in mitigating future defects and provide a basis for creating worst-case situations to browse for possible defense mechanisms.Certainly the most significant social attack on the Bitcoin neighborhood and development procedure happened in 2015 when two well-respected and seasoned Bitcoin designers at that time, Gavin Andresen and Mike Hearn, created and promoted a new, incompatible Bitcoin customer identified Bitcoin XT. Bitcoin XT proposed increasing the possible deals per block, referred to as the blocksize, as a means of taking on conventional payment systems such as MasterCard or Visa. By adopting this incompatible variation of Bitcoin, users would effectively hardfork, or make legitimate, formerly invalid blocks and deals which eventually forces everybody to update their clients similarly– else running the risk of network stability and replay attacks.Bitcoins developer, the anonymous Satoshi Nakamoto, had long considering that stepped away from Bitcoin when this controversial task was revealed and the community was left to decipher Satoshis comments for assistance as though they were sacred writ. Bitcoin XT failed to gain consensus as it naively proposed increasing the optimum blocksize and its supporters looked for to subvert user agreement through closed-door, developer-miner-corporation collusion. Without entering every minute detail of the infamous “blocksize war” and generating an entire book, we can plainly observe from the intensive two-year squabble the important function of complete nodes (users) coordinating to impose brand-new rules without support from miners by means of user-activated softforks (UASF). Had Bitcoin fallen under the huge block trap, network decentralization and Bitcoins apolitical nature would have suffered appropriately. To comprehend the ramifications of changing an apparently basic variable, that being the blocksize limitation, requires not only understanding the technical influence on the codebase stability, but likewise hidden consequences inviting additional attack vectors against the nascent network ecosystem. One can extend this line of thinking toward todays asinine ideas of shifting Bitcoin to proof-of-stake in lieu of proof-of-work. Even though the solution to the blocksize war was dealt with technically through a UASF, the social drama that occurred required non-technical solutions of merely remaining company and not budging on a damaging software application implementation, no matter the business or star developer backing.Attacks By BIP Activation MethodDashjr contends an attack on the Bitcoin Core development procedure happened just last year: the “Speedy Trial” activation technique of the much-anticipated “Taproot” softfork upgrade (BIP 343). The Speedy Trial reasoning works to activate a BIP application without the risk of an unwanted chain divided by means of either rapidly prospering or quickly stopping working to trigger within a three-month timeframe. When the work to construct Taproot was completed, the designers could not come to general contract on the activation technique and basically ignored the essential step of first receiving undoubtable community consensus.Although Taproot effectively triggered and the subsequent functions provided were absolutely helpful for users, its activation method was perceived as questionable and positioned potential vectors of attack while setting bad precedence for future BIP activations. The Speedy Trial activation system was seen as an attack on the Bitcoin Core development procedure since some developers stepped away from the viewed neighborhood agreement while declining to consider BIP 8 as an activation method, otherwise known as the “Lets see what occurs” proposal, in the deployment of Taproot.The Speedy Trial approach was antithetical to the blocksize war outcome, where the fight concluded that users collaborating near-unanimous arrangement ought to manage the network consensus guidelines and not the miners. With Speedy Trial and without BIP 8, the decision to activate (or not activate by just not signaling when its deployed) entirely depended on the miners no matter user consensus. The probably careless Speedy Trial release technique went against viewed neighborhood consensus and, to mitigate this in future, would possibly need coordination of a UASF with sufficient viable adoption beyond a couple of concerned people in the corner of a space to counter a BIPs activation.The panelists at “Preventing Attacks On Bitcoin” thought about how to examine these historic attacks and avoid comparable attacks in future. The “aggressors” promoting Bitcoin XT or Speedy Trial might not have had harmful intent with their proposals, yet plainly their techniques contravened certain principles which a part of the neighborhood adamantly safeguards– that is, the users have the sole right to approve or ban modifications to the agreement rules. In hindsight, the assaulters simply did not follow the very same concepts of Bitcoin that the community did, which led to those attacks ending up being a subjectively interpretive war of what was “best” for Bitcoin.The aforementioned Bitcoin XT and Speedy Trial circumstances convey the techniques in which Bitcoin Cores development procedure might be made controversial, highlighting the necessity to approach all BIP executions carefully and thoughtfully. In the following areas, the panelists think additional possible attack vectors.Bitcoin Software Verification AttacksBishops interests in the development process consist of deterministic builds and construct signing which can be leveraged to prevent particular attack vectors on Bitcoin users, namely attacks that look for to trick the user into believing they have actually downloaded an authentic Bitcoin Core client.Anyone who is a user of a Bitcoin customer need to download it from somewhere on the spam-ridden web. If the web page hosting the download file is jeopardized or intercepted during download, then the file itself might have been maliciously modified. How can that user show the variation they downloaded is certainly the designated Bitcoin client?The typical technique to provide non-repudiation of a software application build, or proof of the integrity and origin of the information, is with digital signatures. Digital signatures, the tamper-proof wax seals electronic and mathematically-inclined cousin, are a basic component of a lot of cryptographic procedures utilizing asymmetric (public and personal) secrets to make it possible for authentication in between two strangers– but wait! This does not ensure signature credibility. Eventually, authentication without self-confidence in the secrets utilized to confirm the signature is meaningless as the recipient need to be guaranteed the confirmation crucial genuinely belongs to the sender.There is then another sly attack vector if the confirmation software application itself is compromised. A clever criminal declaring to be somebody who they are not, but having to likewise show their claim through a digital signature, might plant the compromised key-verifying software application for the unsuspecting user to download and subsequently be presented with a false outcome of authentication. The compromised software contains a very subtle bug that, at a fast look of the code, would manipulate the user into thinking the confirmation software yielded an accurate result.While deterministic builds do not fix authentication of digital signature belongings, it does work to lower the trust needed in a single source or claim to the software application a user has actually downloaded. Deterministic builds work to secure the software application execution versus a couple rogue developers or a jeopardized designers secrets during the advancement procedure. This security is achieved through cryptographic hashes of the software application that designers digitally sign as the software application is constructed throughout each action of the build procedure– successfully making sure that the final software binary files are the exact same as the binary files that the honest designers constructed and for that reason hasnt been jeopardized in any type or fashion.Altogether, with deterministic builds and develop signing, one can basically trace trust in the software application from the binaries to the source code to the git commits made by various designers and recognize what modifications were presented by whom. The legitimacy of the software application can then be even more examined through techniques like web of trust where users can arbitrate whether or not the secrets being confirmed are authentic and they are running the designated Bitcoin client. Therefore, without benefiting from deterministic builds and build signing, the user is prone to a myriad of attack vectors.One such example: if a user downloads a Bitcoin customer through HTTP in lieu of HTTPS with a public Wi-Fi connection, maybe at a foreign coffeehouse or hotel, while not confirming the develop signing, then aggressors might extremely well obstruct the users download connection and replace the download file with an atrocious variation of Bitcoin that might take coins, spy on users, or perform other damaging functions.Bishop finds that a “fun” part of the software application building process is maintaining consistent advancement environment variables which work to remove any sources of non-determinism. Non-deterministic sources might result in unwanted variabilities of the develop signing due to the naturally open environment designers are building on. An irregularity, like varying operating systems between specific designers, produces a completely different hash at the end of the advancement process. Preferably, removing all sources of variability in the develop environment would improve deterministic builds and consequently improve trust in their integrity.Deliberate Ossification Of Bitcoin DevelopmentLopp, directing his inner Sun Tzu, designs an especially devious approach of dividing and controling Bitcoin Core à la wicked designer(s) sowing discontent throughout the neighborhood and GitHub repositories. If a respected developer were to convey severe irritation and anger towards any and all protocol modifications, enhancements or spots, then the growing general consensus will be among worry towards touching the protocol. This “freezing” of the development process is called ossification and would make ongoing procedure enhancements practically impossible.Perhaps accomplishing ossification is ultimately useful for the protocol considering that this would imply Bitcoins extensive recognized dominance, yet Lopp argues just the opposite because ossification is an exploitable attack vector rather than an efficient defense. While ossification works to prevent harmful modifications to the Bitcoin procedure, such as Bitcoin XT, it could likewise work to prevent advantageous or necessary updates that provide increased peer-to-peer privacy and more robust codebase improvements.The attack vector Lopp describes would be extremely hard to assess on the area whether an active confrontation in the development procedure is an attack on the protocol or a legally useful difference. This speaks to the previous point where, in hindsight, the attack is far more visible after the truth. Without having total omniscience of each designers real intent, the development procedure would be stuck between a rock and a hard place.Defense versus technical attacks, like the above-mentioned early bugs and oversights, are relatively straightforward and logical in their solution. When introducing the erratic, human aspect, however, we start playing an unsafe video game with far less predictability. Socially-engineered attacks are frequently packaged with fuzzy solutions and will likely have to be dealt with as they come. A targeted traditional or memetic narrative attack can be totally inconspicuous and figuring out a defense versus them is mainly a gray area.Warfare is the approach of deceptiveness. Arguably, the most rational attack vector for potential foes may be to incite social discontent and meme warfare. Lopp explains that deliberately forcing ossification is the ideal attack because lots of users would consider it a defense.Judicial Attacks On Bitcoin Core DevelopersThe continued frequency of Craig Wright, a specific declaring to be the anonymous Satoshi Nakamoto, and his cryptographic antics plus judicial intimidation of Bitcoin Core developers represents a direct attack on the Bitcoin Core advancement procedure. In spite of the mounting evidence that Craig Wright is not Satoshi Nakamoto, he continues to create chaos by acquiring countless dollars in legal fees and effectively outbidding the defense because of the astronomical expenses– personal and monetary– that Craig Wright imposes on volunteer developers and factors through Strategic Lawsuits Against Public Participation (SLAPP fits). Recall the smart criminal declaring to be somebody who they are not, but needing to also show their claim through a digital signature; this exact situation played out however, due to the abstruse nature of uneven cryptography, has actually been ineffective in encouraging the judicial system.Consequently, Bitcoin Core developers ought to embrace anonymous contribution methods or risk being targeted by a expensive and burdensome lawsuits process. These methods of anonymity ultimately depend on the persons personal privacy practices, perhaps such as avoiding Bitcoin 2022 and conferences completely to maintain privacy. Yet litigation versus an allegedly anonymous person might still be possible if there is an IRL name or personally-identifying element connected to that developers pseudonym. The requirement for contributing privately is itself a future and present problem on designers and their families.Eventually, if these judicial attacks on Bitcoin Core factors persist or Jack Dorseys Bitcoin Legal Defense Fund runs dry, developers will be pushed out of the space and further intensify protocol ossification given that burning money in endless lawsuits is not very appealing; a “death by a thousand cuts,” as Shinobi eloquently summed up it.Future Attacks And Complications In Bitcoin DevelopmentIf Bitcoin is anticipated to make it through and prosper not just in this century, however for lots of centuries and so on, then careful steps must be taken in formulating defense mechanisms versus expected and unforeseen attacks on Bitcoin Core as well as the Bitcoin environment. You cant have a multi-generational wealth automobile if it ends up being useless before you die.While the panelists held differing views on whether attacking Bitcoin users is comparable to assaulting the Bitcoin procedure, there continue to exist vectors of attack on the users, like the aforementioned deceitful digital signatures and the continuous Craig Wright legal legend. Other vectors include bad wallet develop practices or malicious mainstream narratives brainwashing users that could be considerably damaging to particular concepts of Bitcoin we find paramount.In spite of advancements in Bitcoin private essential management, known as wallets, there remains the possibility of bad actors intentionally developing wallets that do not follow the most current nor ideal security practices available to them. There are still wallet executions that use a single address to get and send bitcoin– therefore exposing any privacy users may have.As well, although not necessarily intentional but rather a result of its limitations, any kind of light wallet (one that does not likewise operate as a full node itself) requires a connection to a complete node in order to interact transactions. Light wallets, particularly popular for casual users, pose the duality of a simple, user friendly user interface, however also present spaces in security ripe for attack vectors. Users of these wallets are prone to their transaction communications being obstructed by possibly dubious actors. A simple solution– but not practical for some– to this vector would be to forego using light wallets in favor of full node wallets.Shinobi visualizes alternative attack vectors originating from plain disinformation projects against Bitcoin and then rapidly spiraling into government lobbying for legal action and heavy policies. One such obvious disinformation project is the unproven notion that proof-of-stake is a feasible option to proof-of-work. If all jurisdictions, mainly those with readily cheap and plentiful energy facilities, fell in a domino-effect of power grabbing desperation to suppress stomp Bitcoin through outright banishment of bitcoin mining, maybe imposed through inspecting special energy grid power modulations that can determine bitcoin mining rigs, then transferring all the existing hash power off-grid would show rather challenging.The process of changing and acquiring the essential scales of energy off-grid– especially in trick– is no easy job. As an example, photovoltaic panels and wind turbines stay far too restrictive to serve as a comparable replacement and completely shoulder a network-wide shift to off-grid bitcoin mining due to solar and winds inherent variable and periodic power generation. Dashjr proposed a prospective option by deviating from the present proof-of-work standard just if the situation were dire enough. If the blockchain were halted from some inconceivable political dictation or the hashing algorithm (SHA256) utilized to secure Bitcoin were broken, then coming together to discover a solution may be possible and would be beneficial for all network participants.This proposal of customizing proof-of-work as we understand it is itself a case-in-point for the unforeseen attacks that could take place on Bitcoin and the undoubtedly questionable decisions through the Bitcoin Core advancement process that would follow provided such an alarming scenario.Continuing down the path of hypothetical scenarios that would require time-sensitive BIP implementations, perhaps the worst-case situation possible would be if the ECDSA, sha256, or ripemd-160 mechanisms were unquestionably compromised– however even then, the concern stays of what would be practical alternatives? Lopp jokes in stating a quantum-proof algorithm will make everybody delighted, but this saucy response will likely become truth eventually in the far future, requiring unsavory difficult fork conversations around practical defense mechanisms versus quantum computing exploiting asymmetric cryptography.Bitcoin is an apolitical cash and tranquil protest versus the corrupt and incumbent financial routine. Because of the nature of the challenger Bitcoin is dealing with, i.e., the U.S. dollar, an unrelenting barrage of social and technical attacks against Bitcoin is likely to happen, if not currently under way. Bishop relates Bitcoins totally voluntary community, who is steadfastly protecting Bitcoin at the prepared, to that of a self-developed “body immune system” that might be Bitcoins greatest defensive and offending mechanism.Closing ThoughtsIn summary, Bitcoin is by no means invincible. Without actively thinking about all potential attack vectors and seeking particular options, the always-waiting adversaries might find weak points in the code or in the community itself. Whether the attack be from colluding celebrations, fake Bitcoin software, intentional ossification, targeted attacks through the judicial system or some unidentified future catastrophe scenario, Bitcoiners need to collaborate and join to seal any spaces that might be the start of completion for Bitcoin.The objective of this panel is not to impart in the audience doom nor gloom, but rather to recommend a proper dosage of reality with the extremely possible attacks Bitcoin development and the network could experience progressing. Disregarding this would be extremely damaging to the overall security of Bitcoin if we decide to live in euphoric ignorance of these attack vectors. Ought to history have anything to teach us, it would be that all existing and previous monetary routines– beyond Bitcoin– have caught the fallibility of human organizations. Lets work to not have Bitcoin experience a comparable fate.Humans are rationally driven by monetary rewards which has allowed the open source, pseudo confidential, monetary nature of Bitcoin to harness a large, skilled group of hackers with opportunity for a benefit of the limited currency that is bitcoin. The discovery and exploitation of defects that could jeopardize Bitcoin would paradoxically diminish the enemys newfound wealth– therefore, in theory, monetarily motivating hackers to constantly support the Bitcoin network and responsibly report bugs and exploits.Despite discussions of methods to attack the Bitcoin Core development procedure and the larger environment with little readily-available services of how to exactly establish and prevent these attacks, Bishop ended the panel with a poignant statement that talked to the greatest reward of all: money. He said, “Bitcoin is the greatest bug bounty program of all time … all the best.”This is a guest post by Okada. Viewpoints expressed are completely their own and do not necessarily show those of BTC, Inc. or Bitcoin Magazine.
“The following is a summary of stated panel with a quick overview of the Bitcoin Core development process.Brief Bitcoin Core OverviewThe Bitcoin Core designers work through an advancement procedure to use the Bitcoin procedure bug spots, software application optimizations and boosted functions; they then publish these updates following community consensus by means of Bitcoin Improvement Proposals (BIPs). The Bitcoin protocol agreement rules need that all Bitcoin financial participants and full nodes invariably implement those rules when thinking about the validity of a block.Additionally, Bitcoin Core updates are not downloaded instantly however rather by hand, as automatic software updates provide an attack vector for a naughty star to jeopardize all the nodes and miners in a single stroke.The Bitcoin Core team of designers do not pedestal a single leader or representative– thus distancing the customer and development process from individual character exploitation due to faults all earthly leaders naturally possess. By comprehending past vulnerabilities and their options, we can stay watchful in mitigating future flaws and provide a basis for producing worst-case situations to browse for possible defense mechanisms.Certainly the most noteworthy social attack on the Bitcoin community and advancement procedure happened in 2015 when two experienced and well-respected Bitcoin designers at that time, Gavin Andresen and Mike Hearn, produced and promoted a brand-new, incompatible Bitcoin client labeled Bitcoin XT. The requirement for contributing independently is itself a future and present concern on designers and their families.Eventually, if these judicial attacks on Bitcoin Core factors persist or Jack Dorseys Bitcoin Legal Defense Fund runs dry, designers will be pushed out of the space and more escalate protocol ossification considering that burning money in unending lawsuits is not really attractive; a “death by a thousand cuts,” as Shinobi eloquently summarized it.Future Attacks And Complications In Bitcoin DevelopmentIf Bitcoin is expected to survive and flourish not simply in this century, however for many centuries and so on, then cautious steps must be taken in formulating defense systems versus anticipated and unforeseen attacks on Bitcoin Core as well as the Bitcoin environment. Bishop relates Bitcoins completely voluntary community, who is steadfastly safeguarding Bitcoin at the all set, to that of a self-developed “immune system” that could be Bitcoins biggest defensive and offending mechanism.Closing ThoughtsIn summary, Bitcoin is by no methods invincible.